Security on the Kyndryl Cloud Uplift Platform
Implementing comprehensive security controls in the cloud
Securely running workloads in a cloud environment requires a multi-layered approach which covers both how workloads are deployed and maintained within your account and the management of your Kyndryl Cloud Uplift account itself. This document outlines architectural elements necessary to achieve a robust implementation on the Kyndryl Cloud Uplift platform and best practices for how to best configure your Kyndryl Cloud Uplift account.
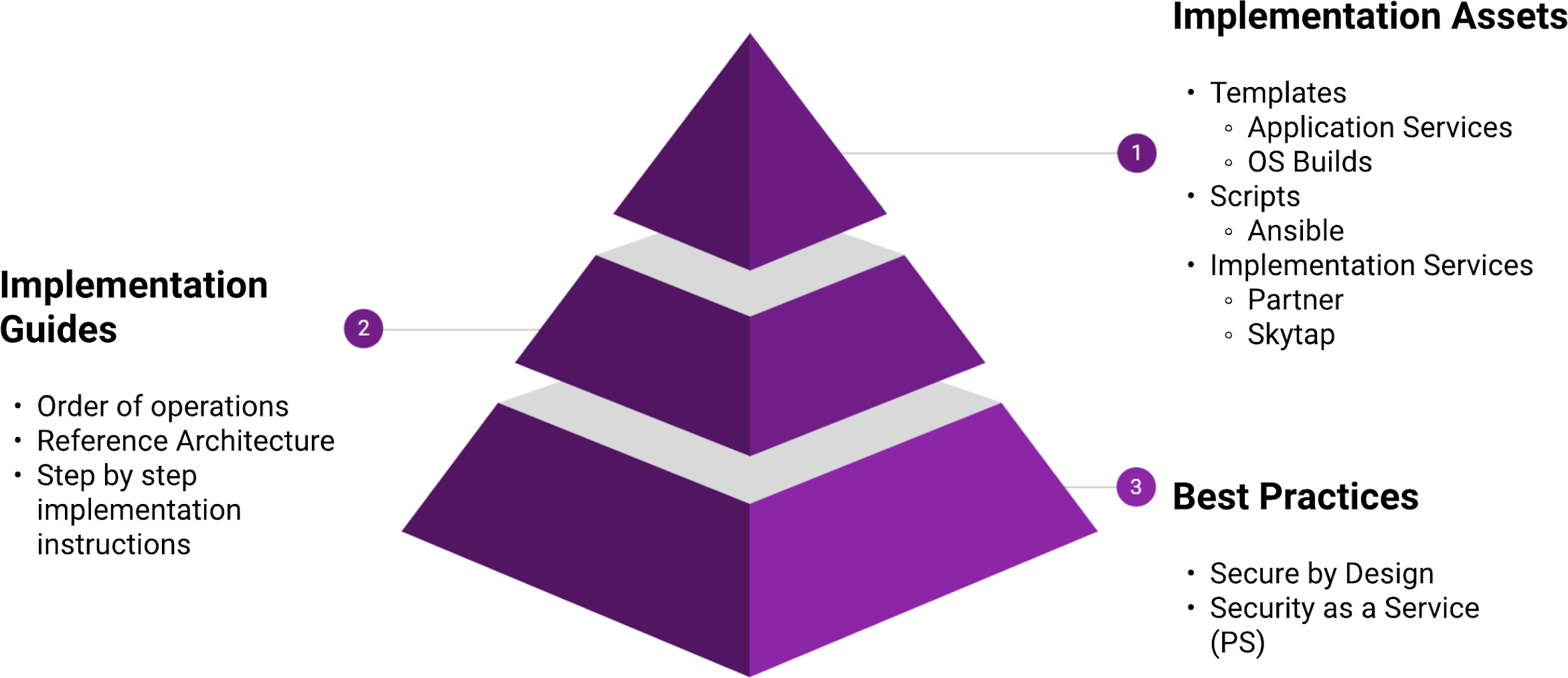
Figure 1 – Control map
Assets you deploy into your account should be defined by implementation standards based on your use cases and requirements, while taking into account best practices of how to leverage Kyndryl Cloud Uplift. Each layer in this model is built on the capabilities delivered in the layer below; you can’t know how to secure virtual machines without understanding how they can be secured, and why they need to be.
Accompanying this document is a Kyndryl Cloud Uplift - Security Controls Workbook that you should refer to as you develop your high-level and low-level designs. The workbook outlines each area discussed herein with specific controls that should be applied. It also contains an example of a risks and mitigations register that you should consider as part of any cloud project.
Similar to other cloud services, Kyndryl Cloud Uplift operates a shared responsibility model with regards to security. Kyndryl Cloud Uplift is accountable for the platform, and customers are accountable for the way they use that platform.
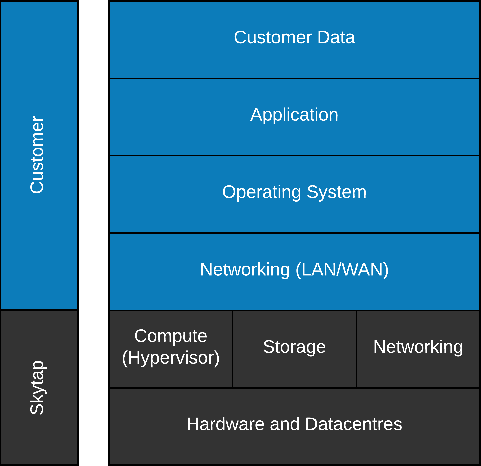
Figure 2 – Shared responsibility model
Additionally, resources deployed into Kyndryl Cloud Uplift should have a clearly defined operating model:
- Who is responsible for creation and deletion of virtual machines?
- Who is responsible for updating the application and data on your virtual machines?
- Who can provide common services support on the virtual machines?
- Are there services external to Kyndryl Cloud Uplift that need to be supported for your workloads?
- Which of your existing operating models need to change for new cloud workloads?
The approach to the cloud must be integrated within your organisation’s Target Operating Model; this allows for the appropriate security controls to be accounted for, architected, and implemented.
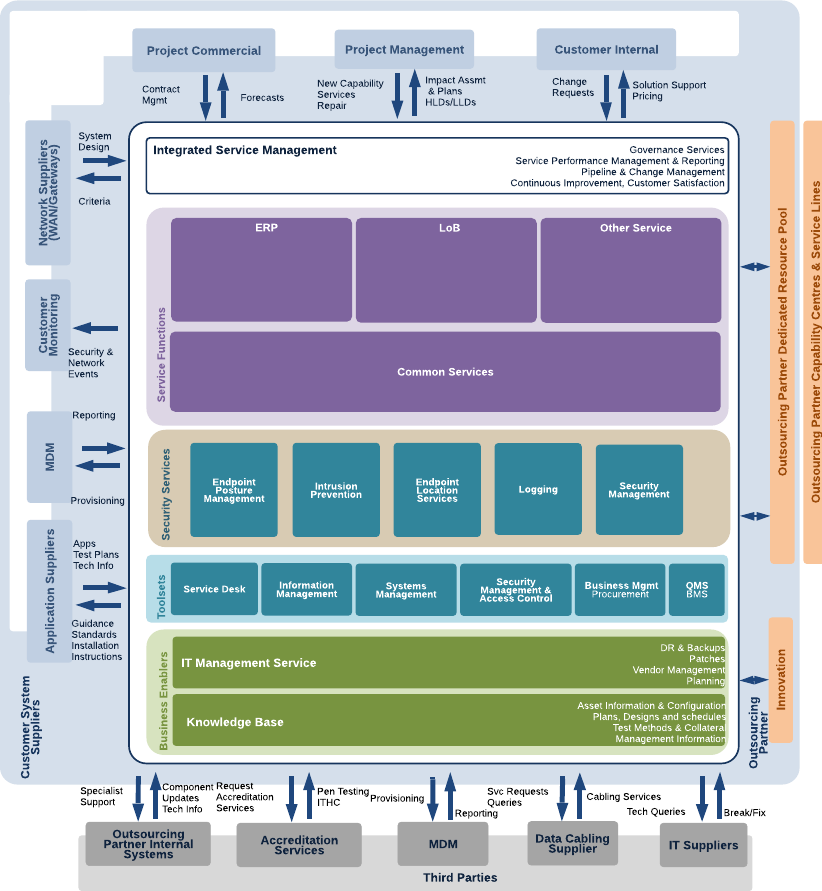
Figure 3 – Example target operating model (TOM)
Most organizations will have multiple cloud vendors, supported by systems integrators or outsourced management functions. Your various clouds need to be managed holistically, but controls applied specifically. For example, all logging across your organization should be consolidated into a single Security Incident Event Monitoring (SIEM) system, but the approach to management and remediation will be custom to each workload and each platform.
